TL; DR: This is a pilot program for Financial Institutions to standardise Threat Intel, Red Teaming, Purple Team and Gold Teaming to understand the financial industries resilience to cyber-attack.
As leaders in offensive security and with my co-founders having come from Red Teams within some of Australia’s leading organisations we took a particular interest when the RBA released the Cyber Operational Resilience Intelligence-led Exercises (CORIE) in late 2020. Having experience delivering these engagements we believe it is a step in the right direction with the end goal being Australian organisations utilising more advanced offensive security services to ensure they are suitably protected.
The below article offers a summary of the framework for ease of reference.
The CORIE framework is a guideline released by the Council of Financial Regulators (CFR) to test the maturity and resilience of Financial Institutions (FI) in Australia. The key objective is to identify systematic weaknesses, assess resilience and then provide remediation plans to the issues identified.
The purpose is to mimic adversaries that are not restricted by time or scope and to give a full understanding of an organisation’s security posture. This is done by emulating Tactics, Techniques and Procedures (TTPs) that are being used in the real world. The results will then be fed back to the CFR who will review and decide the best actions following the pilot. This may include expanding the program to other FI’s or other industries.
The following article provides a summarised version of the guideline. The full version of the guideline can be viewed here.
The framework covers four key services which are:
- Threat Intelligence
- Purpose is to identify adversaries targeting FI, understand modus operandi, gather info, and provide FI with an understanding of the information available about them.
- Adversary Attack Simulation – Red Team Exercise
- Assess people, processes, and technology
- Reveal attack paths that have not been considered and understand maturity of target
- Red team needs to be via an external provider, others can be in house.
- Replay Adversary Attack Simulation – Purple Exercise
- Replay attack simulation and provide knowledge on how to address the requirements.
- Opportunity for Blue Team to learn from the successful attacks to help with remediation
- Crisis Simulation Tabletop – Gold Team Exercise
- Incident response planning and management for Executives
Currently Purple and Gold Team are not requirements under the pilot program, but information on how to perform these is included in the guideline. Depending on the success of the pilot it may be mandated or pushed to other industries.
The focus of the document is on the Threat Intelligence-led Adversary Attack Simulation (Red Team).
Providers
Providers under the CORIE guideline should provide suitably qualified consultants to complete the work. An example of some relevant certifications is below.
- CREST Certified Threat Intelligence Manager (CCTIM)
- CREST Certified Simulated Attack Manager (CCSAM), or
- SANS SEC564: Red Team Ops and Threat Emulation (No Certification),
- CREST Certified Simulated Attack Specialist (CCSAS)
- CREST Certified Infrastructure Tester (CCT Inf)
- Offensive Security Certified Expert (OSCE)
- Offensive Security Certified Professional (OSCP)
- GIAC Advanced Penetration Tester (GXPN)
The typical Red Team would consist of:
- Red Team Lead
- Red Team Specialist
- Exploit Development Specialist
- Red Team Member – various team members depending on skills required
Full details are outlined within the guidelines.
Red Team
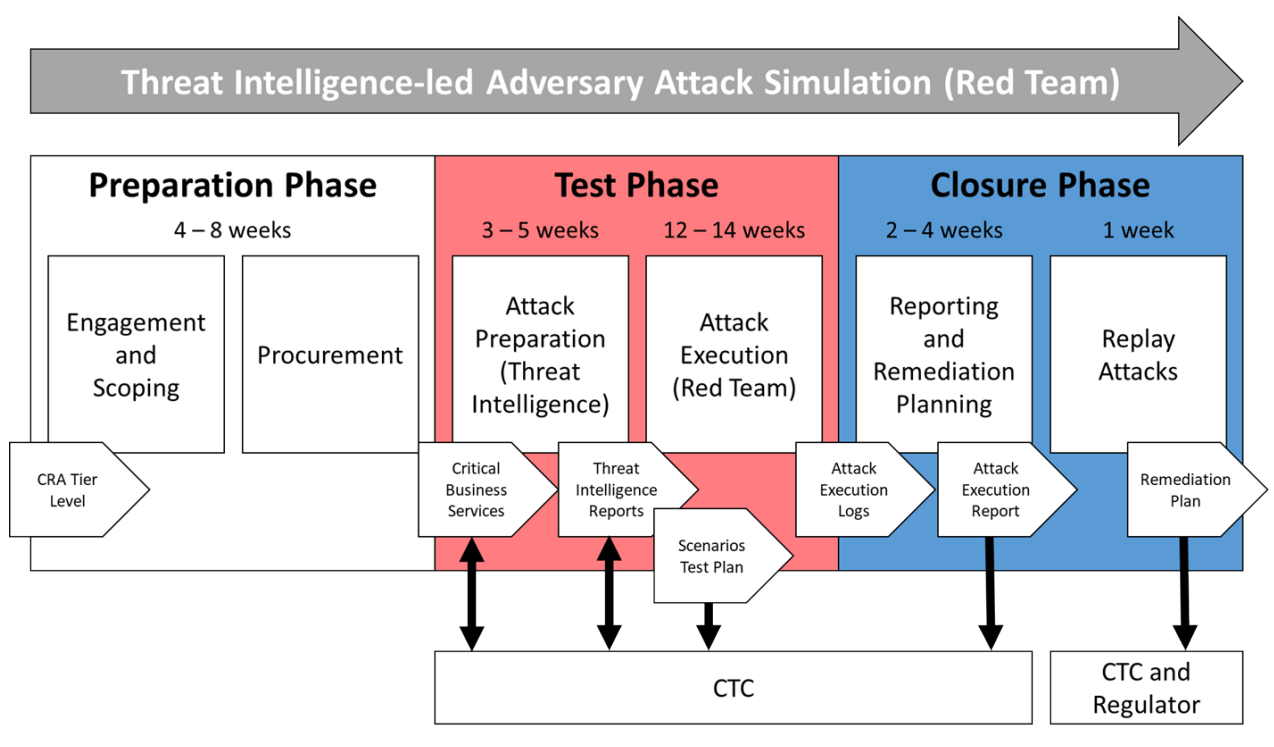
The below diagram provides an overview of the various phases of the Red Team:
Figure 1. The Threat Intelligence-led Adversary Attack Simulation is split into three phases to be completed over multiple months.
The standard has a few scenarios that should be developed with the assistance of threat intel. They cover:
- A Nation state gains access via social engineering (i.e. spear phishing, watering hole). From the initial foothold they escalate privileges and avoid detection until they gain control over their target.
- Organised Crime using ransomware via a number of attack vectors including wireless, physical access and social engineering.
- Organised Crime gaining access to a physical device and attempting to steal information from the device. The device can be powered off, or if targeted enough they could potentially steal an unattended device still connected to the corporate VPN.
Scope and Execution of the Red Team
FI’s will be classified according to different tiers. The scope of the different tiers is:
- Tier 1’s must do at least 3 scenarios (1 provided by regulator) targeting 2 critical business services. Engagement length 90-120 days
- Tier 2’s must do at least 2 scenarios (1 provided by regulator) targeting 1 critical business service. Engagement length 80-100 days
- Tier 3’s must do 1 generic scenario provided by the regulator. Approximately 60 days for the engagement.
Red teaming every other year with purple and gold teams in between.
- Tier 4 only does Purple and Gold exercises.
Critical Business Services
Business services are not an individual system but rather a composite of an FI’s people, processes and technology supporting a service Each FI should identify all business services and order them by risk. They should then identify which business services will be in scope for the exercise.
Test Phase
This section outlines broadly the test phase of the Red Team.
Attack Preparation – Determining the scenarios that will be simulated in the test phase. This can be led by threat intelligence from internal sources, government sources or from the Red Team. This should include scenarios, test plans and flags (objectives) of the test.
Attack Execution – Red team taking action and is expected to be between 12-14 weeks depending on number of scenarios and business services in scope.
Communication Plan - On the FI side there should be a white team who are the points of contact for the red team. It is important that communication channels are established prior to the engagement and adhered to during to protect the secrecy of the exercise. This should also include regular update meetings.
Attack Execution Log – A log of all activities undertaken during the test should be recorded for future reference. This should also include cleanup steps.
Concessions – Red teams may need assistance to progress if they are stuck during an engagement. Concessions may be the provision of extra information, access to a certain system or some type of credentials. Any concession should be recorded and included in the report. Detection and Response – The Red Team can measure the effectiveness of the Blue Teams response. If they remain undetected through the engagement, they can make increasingly noisy actions until detected.
Closure Phase - This encompasses reporting, remediation, and planning.
Replay Attacks – As part of the project closure the Red Team can replay attacks with the Blue Team to give the Blue team the opportunity to improve their practices and identify where there are opportunities for improvement. These should be plotted against recognized attack frameworks. This would typically take between 2 – 5 days.
Replay Adversary Attack Simulation - Purple Team Exercise
These would typically run for 7-14 days and can be run by an external provider or internal team. This is not in scope for the CORIE pilot program. Like the replay attacks described above these simulations involve a Red Team working with the FI’s defensive (Blue) team to repetitiously execute adversary’s tactics, techniques, and procedures against the FI’s defences. This is a learning opportunity for the Blue Team.
Crisis Simulation Table Top - Gold Team Exercise
This is a crisis simulation tabletop to improve communications, crisis management procedures and decision making in preparation for a cyber incident. This is not in scope for the CORIE pilot program.
Partner’s for CORIE Delivery
The CORIE framework is designed to be delivered by consultants with specialised skills. For this reason it is important to assess the skill sets of the team delivering the work to ensure that they have suitable qualifications and most importantly experience in delivering advanced red team services. Along with certifications look for consultants who are able to demonstrate a few of the following, they have been part of internal Red Teams, have experience with CORIE, have presented on Red Team related topics and can demonstrate a clear understanding of the required methodology.
Summary
The CORIE Framework is the first step in having a unified framework for adversary led security testing of organisations within Australia. It significantly leverages the experience from overseas markets such as CBEST in the UK, Singapore ABS Red Team Guidelines and the TIBER-EU Framework from the European Central Bank. Using those markets as a guideline it can be expected that this pilot will eventually become a requirement and expand across other critical industries in Australia. While the cost of the engagements may at first seem prohibitive to some organisations, the overall benefit in reducing the likelihood of a successful attack and improving defences will most likely far outweigh the costs.
About the Author
Marco Cantarella is one of the co-founders and Commercial Director at Tanto Security. He has worked in cyber security for over 10 years on the operations and commercial side of penetration tests, compliance, incident response and red teaming. You can connect with him on LinkedIn or get in touch at marco@tantosec.com or 1300 182 686.