TL; DR: Match the type of security services you are using to the level of maturity and the types of threats that your organisation faces to ensure you meet your objectives.
Engaging offensive security services is a vital part of most organisations’ cyber security strategy. One thing that we are often talking about with customers is the type of services you should be engaging as these are not the same for everyone. We encourage a pragmatic approach to the procurement of offensive security services that takes into account the threats faced, the level of maturity and the internal capability of the organisation.
This article looks to outline (at least partially) which services you should consider depending on the level of maturity of your organisation.
Where to start - Maturity and Understanding Threats
The purpose of this post is to provide a guideline for which services could be relevant based on maturity. Security maturity can be an arbitrary measure determined by those in the organisation who are most qualified, although we strongly suggest measuring it against industry standards. Typically the standards referenced are either the ASD Essential 8 Essential Eight | Cyber.gov.au or the standards from NIST. These standards and most practical security advice centres around understanding the current level of security and then making decisions via cost-benefit analysis to determine where resources can be best spent to reduce risk.
Understanding the level of maturity, whether it be against a formal standard or based on experience, will assist in helping to develop the offensive cyber security services program of an organisation. Another measure which can be hugely helpful is spending time understanding the potential threats that your organisation faces. Threat modelling is a topic that I have become increasingly interested and I am constantly learning more about. Fortunately there are a lot of smart people in this field who are very generous in sharing information. If you are looking to start introducing threat modelling but don’t know where to start I would highly recommend the Fast, Cheap + Good Whitepaper from Adam Shostack.
These activities will help to understand where to start. Naturally the more mature an organisation and the more time and resources invested in defence the more advanced the type of service needs to be to ensure there is a benefit to conducting the service. These two factors discussed above will not be the only ones as other things such as budget, timelines and compliance requirements will also have an impact in determining what needs to be delivered.
Planning Offensive Security Service
Once you have a bit of an understanding of the threats faced and the level of maturity within the organisation we can start to plan the types of services required.
Scope
Deciding where to focus the testing will have an impact on the relevant services.
- Want to focus on internet facing systems? Then pen testing is a great place to start.
- Concerned about threat actors inside the network? Then assumed breach scenario testing would be most relevant.
- Want to really understand how secure you are against a motivated and skilled adversary? Then you are probably ready for red teaming.
The number of systems, the type and how they are accessed will have an impact on the services to be delivered. At this stage knowing what information is most important to the organisation and where it resides can make planning services and deciding which systems should be in scope easier.
A note on skill sets
As the level of maturity increases and the services delivered become more advanced it is vital to understand the skill sets of the consultants assigned to deliver the work. This helps to ensure that the objectives agreed prior to the start of the engagement can be achieved. Experience is a strong indicator including previous roles, projects and aligned interests (i.e. research, bug hunting, CTF’s). Good security testers will think creatively and challenge systems in ways other people may not. This by its nature means that reporting will be exception-based with only found vulnerabilities reported. For this reason we encourage an understanding of the background of the consultants delivering the work prior to starting to ensure they are suitably experienced and qualified because once the reports have been delivered it will be too late.
Which Service
So we have an understanding of the level of maturity and the threats that are faced. We can start to estimate the services that are going to be most relevant. This is by no means a definitive list but can help act as a guide during the planning stage.
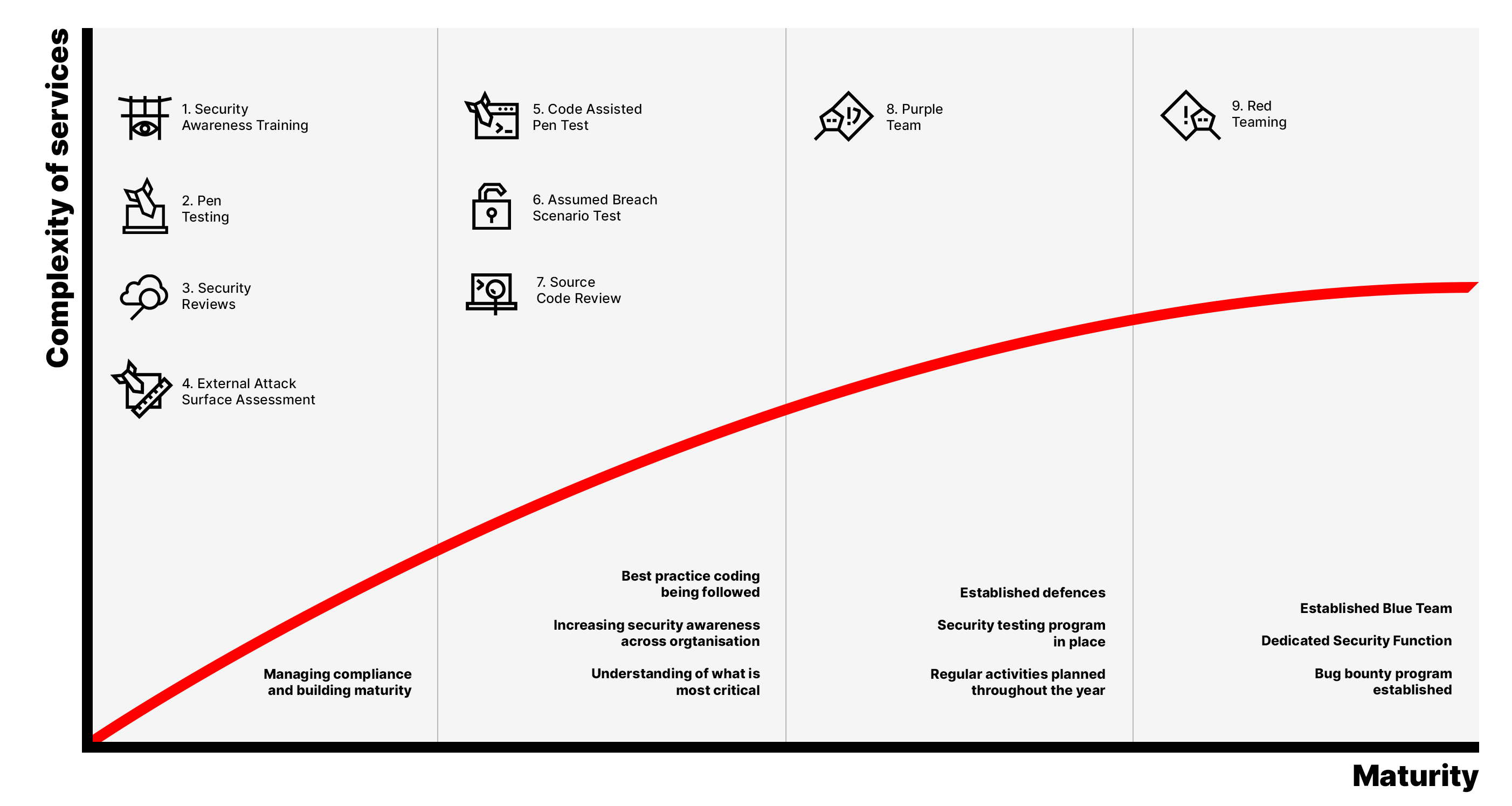
The graph below starts to attempt to classify services that would be relevant based on the level of maturity with the complexity of services being shown on the X axis. Beneath the arrow I have included some points of reference for what we would expect to see at the corresponding level of maturity.
Figure 1. Complexity of services mapped to level of maturity.
I recognise a number of these could easily be shifted around or moved. There is a degree of simplicity that I have applied to make the graph more digestible. For example the complexity of penetration testing can vary greatly as testing a brochureware site is much more straightforward than testing an application that handles complex financial transactions. For web applications in particular OWASP has the Application Security Verification Standard which can help guide how in depth your penetration testing should be.
As you can see the most complex of services are Purple Team and Red Team. For the cost benefit analysis to balance on these services the company does need to have spent some time maturing and developing their own internal defences. Performing a Red Team when there is no monitoring and alerting in place for instance might lead to a report with lots of alarming sounding vulnerabilities, but in practical terms it could take the team years to build up defences that will address those findings. That time and resources consumed trying to respond to the findings of the report could have been better spent pragmatically planning and making risk based decisions on where to build security maturity within the organisation.
As you move along the maturity axis you may look to engage certain services less. An example of this is as your DevSecOps practice matures and you continue to ‘shift left’ the need for more static and standard security offerings will reduce. This allows you to focus the resource savings to other areas of your security program that are going to provide a greater benefit.
Implementing a Testing Program
While there may be occasions where a security service is urgently required - for example a key customer demanding a certain action, the best approach is to plan and develop a testing program and offensive security services that go hand in hand with the level of maturity of the organisation and the threats faced. The previously mentioned standards from the ASD and NIST are great points to start working on lifting the security maturity of an organisation.
Security is an ongoing program of works and offensive security forms one part of a larger trove of activity that the best organisations in the world undertake. The defining factor of all of these successful programs is that they are never static, there is always something that can be refined and tweaked to ensure continued success.
Using trusted partners who can advise on what other customers are doing with their offensive security programs is another great resource to be utilised. These organisations would have delivered all of the services that I have outlined so can typically gauge from a few conversations what services are most appropriate.
If you enjoyed the article or have thoughts, criticisms or general feedback I would love to discuss these concepts more. You can email me at: